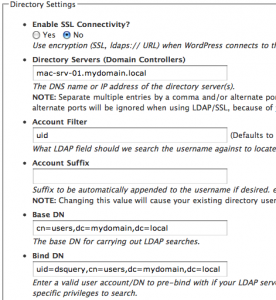
Today I had to login into one of my WP powered weblogs, running the wpDirAuth 1.3 plugin which I wrote about in this previous post. Surprisingly, it returned me the error message “No directory server available for authentication”. No change was made in the last few days in my infrastructure, and I soon discovered that all user accounts in my Active Directory were able to succesfully authenticate with the only exception of mine!
A few minutes have been necessary to understand that the problem was lying in the password I changed yesterday, which was including an apostrophe (‘). It seems that the function parsing this variable in WordPress automatically puts a backslash (\) escape character before the apostrophe, in order to pass it correctly to the builtin authentication function. The matter was the way the ldap_bind() PHP function was sending the password to my domain controllers, including the unnecessary (in this case) escape character.
I’m not a developer, but I think I resolved this issue, simply by adding the line in bold to the wpDirAuth_bindTest() function in the file wpDirAuth.php:
function wpDirAuth_bindTest(&$connection, &$username, &$password)
{
   $password = strtr($password, array(“\'”=>”‘”));
   if ( ($isBound = @ldap_bind($connection, $username, $password)) === false ) {
     // @see wpLDAP comment at http://ashay.org/?page_id=133#comment-558
     $isBound = @ldap_bind($connection,”uid=$username,$baseDn”, $password);
   }
   return $isBound;
}
Since the returned error message was also incorrect (it should be a “check credentials” warning, not a “server unreacheable” error), I’ve also included the change suggested by Clint in the last part of his message “I have a bug fix for 1.3…“.
I’ve also succesfully tested this modified wpDirAuth plugin against different Active Directory instances on WordPress 2.6 and I’ve genereted two patch to upgrade from both 1.2 and 1.3 version. Here are the links:
If you prefer to use directly the 1.4 release I’ve also prepeared a pre-patched copy that you can download it here.
Since that’s not my job, I’m not sure to have done a good thing by defining this as the new 1.4 release, and I’ll be glad to receive any suggestion about it.