After a couple of days spent in studying and testing, today the first SVN server was put in the development stage. A test repository is available for anonymous checkout and ViewVC browsing at http://svn.valsania.it. Commit privilege is granted only to selected accounts, defined both in Active Directory and htpasswd file.
This first deployment still has some rough corners, but the main goals are targeted:
- simple anywhere access to the repository both for read and write access (via WebDAV and ViewVC);
- secure transmission of credentials and data (enforced SSL offloading was activated);
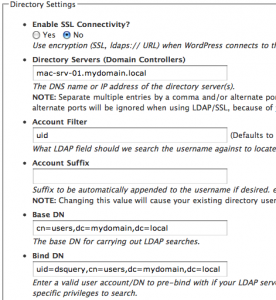
- integrated authentication with corporate directory service (thanks to the auth_ldap Apache module).
During the next days I’ll be committed to put this service in the hands of all the developers which have the potential to be involved in any sort of collaboration with our company in the future!